Which Security Measure Is Typically Found Both Inside And Outside A Data Center Facility?
More Questions: Network Security ( Version one) – Network Security 1.0 Terminal Exam
1. In the video that describes the anatomy of an attack, a threat thespian was able to gain access through a network device, download data, and destroy it. Which flaw immune the threat actor to do this?
- a flat network with no subnets or VLANs
- improper physical security to gain admission to the edifice
- lack of a strong password policy
- open ports on the firewall
Hint/Explanation: The company had a flat network with no subnets. The threat actor was able to access and destroy all kinds of corporate data due to a thermostat that was on the network, but was not scanned as part of the security procedures.
2. What method tin be used to mitigate ping sweeps?
- blocking ICMP echo and echo-replies at the network edge
- deploying antisniffer software on all network devices
- installing antivirus software on hosts
- using encrypted or hashed authentication protocols
Hint/Explanation: To mitigate ping sweeps, ICMP repeat and echo-reply messages can be blocked on network edge routers. This does come at a price. Because ICMP is too used for network diagnostic data, this diagnostic data will exist blocked as well.
3. When the CLI is used to configure an ISR for a site-to-site VPN connectedness, which two items must be specified to enable a crypto map policy? (Choose two.)
- the hash
- the peer
- encryption
- the ISAKMP policy
- a valid access listing
- IP addresses on all active interfaces
- the IKE Phase 1 policy
Hint/Explanation: After the crypto map control in global configuration mode has been issued, the new crypto map will remain disabled until a peer and a valid access list have been configured.
4. How does a firewall handle traffic when it is originating from the public network and traveling to the DMZ network?
- Traffic that is originating from the public network is inspected and selectively permitted when traveling to the DMZ network.
- Traffic that is originating from the public network is usually permitted with little or no restriction when traveling to the DMZ network.
- Traffic that is originating from the public network is usually forwarded without inspection when traveling to the DMZ network.
- Traffic that is originating from the public network is usually blocked when traveling to the DMZ network.
5. Refer to the exhibit. A corporate network is using NTP to synchronize the time across devices. What can be adamant from the displayed output?
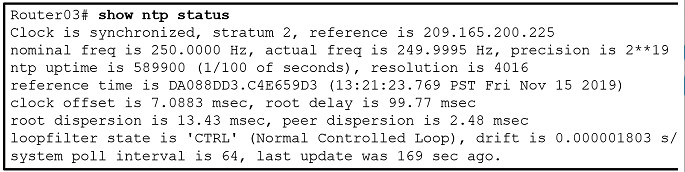
- Router03 is a stratum 2 device that can provide NTP service to other devices in the network.
- The time on Router03 may not be reliable considering it is offset by more than than seven seconds to the time server.
- The interface on Router03 that connects to the fourth dimension sever has the IPv4 address 209.165.200.225.
- Router03 time is synchronized to a stratum ii time server.
six. When describing malware, what is a difference between a virus and a worm?
- A virus focuses on gaining privileged access to a device, whereas a worm does not.
- A virus replicates itself past attaching to another file, whereas a worm can replicate itself independently.
- A virus tin can be used to launch a DoS attack (but not a DDoS), but a worm can be used to launch both DoS and DDoS attacks.
- A virus can be used to evangelize advertisements without user consent, whereas a worm cannot.
Hint/Explanation: Malware tin can be classified as follows:
Virus (cocky-replicates past attaching to another program or file)
Worm (replicates independently of another program)
Trojan horse (masquerades as a legitimate file or plan)
Rootkit (gains privileged access to a machine while concealing itself)
Spyware (collects information from a target system)
Adware (delivers advertisements with or without consent)
Bot (waits for commands from the hacker)
Ransomware (holds a computer system or data captive until payment isreceived)
7. Which blazon of packet is unable to exist filtered past an outbound ACL?
- multicast packet
- ICMP packet
- circulate packet
- router-generated packet
Hint/Explanation: Traffic that originates within a router such every bit pings from a control prompt, remote admission from a router to some other device, or routing updates are not affected past outbound admission lists. The traffic must flow through the router in order for the router to apply the ACEs.
8. What are two methods to maintain document revocation status? (Cull ii.)
- subordinate CA
- OCSP
- DNS
- LDAP
- CRL
Hint/Explanation: A digital certificate might demand to be revoked if its key is compromised or it is no longer needed. The certificate revocation listing (CRL) and Online Certificate Condition Protocol (OCSP), are two common methods to check a certificate revocation status.
9. Which protocol is an IETF standard that defines the PKI digital certificate format?
- SSL/TLS
- 10.500
- LDAP
- X.509
Hint/Explanation: To address the interoperability of dissimilar PKI vendors, IETF published the Net X.509 Public Central Infrastructure Certificate Policy and Certification Practices Framework (RFC 2527). The standard defines the format of a digital certificate.
ten. A network ambassador is configuring DAI on a switch. Which command should exist used on the uplink interface that connects to a router?
- ip arp inspection trust
- ip dhcp snooping
- ip arp inspection vlan
- spanning-tree portfast
Hint/Explanation: In general, a router serves equally the default gateway for the LAN or VLAN on the switch. Therefore, the uplink interface that connects to a router should be a trusted port for forwarding ARP requests.
11. Consider the admission list command practical outbound on a router serial interface.
access-list 100 deny icmp 192.168.10.0 0.0.0.255 any repeat answer
What is the effect of applying this access listing command?
- The just traffic denied is repeat-replies sourced from the 192.168.x.0/24 network. All other traffic is allowed.
- The just traffic denied is ICMP-based traffic. All other traffic is allowed.
- No traffic will exist immune outbound on the serial interface.
- Users on the 192.168.10.0/24 network are not allowed to transmit traffic to any other destination.
12. Which control is used to activate an IPv6 ACL named ENG_ACL on an interface so that the router filters traffic prior to accessing the routing table?
- ipv6 access-class ENG_ACL in
- ipv6 traffic-filter ENG_ACL out
- ipv6 traffic-filter ENG_ACL in
- ipv6 access-form ENG_ACL out
Hint/Explanation: For the purpose of applying an access listing to a item interface, the ipv6 traffic-filter IPv6 command is equivalent to the access-grouping IPv4 command. The direction in which the traffic is examined (in or out) is too required.
13. A client connects to a Web server. Which component of this HTTP connection is not examined by a stateful firewall?
- the source IP address of the client traffic
- the destination port number of the customer traffic
- the actual contents of the HTTP connection
- the source port number of the client traffic
Hint/Explanation: Stateful firewalls cannot forestall awarding layer attacks considering they do not examine the actual contents of the HTTP connexion.
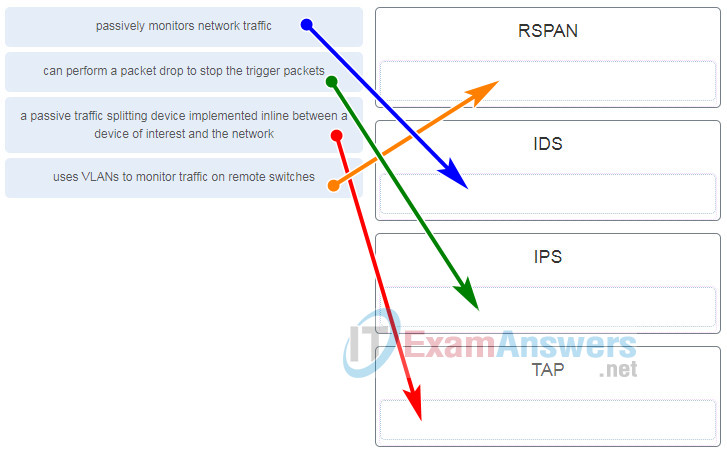
14. Which network monitoring technology uses VLANs to monitor traffic on remote switches?
- IPS
- IDS
- TAP
- RSPAN
Hint/Explanation: Remote Bridge (RSPAN) enables a network administrator to use the flexibility of VLANs to monitor traffic on remote switches.
fifteen. Which dominion activity volition cause Snort IPS to block and log a package?
- log
- drop
- alert
- Sdrop
Hint/Caption: Snort IPS style can perform all the IDS actions plus the following:
– Drop – Block and log the parcel.
– Reject – Cake the bundle, log information technology, and and then send a TCP reset if the protocol is TCP or an ICMP port unreachable message if the protocol is UDP.
– Sdrop – Cake the packet but do not log it.
16. What is typically used to create a security trap in the data center facility?
- IDs, biometrics, and ii admission doors
- high resolution monitors
- redundant authentication servers
- a server without all security patches applied
Hint/Explanation: Security traps provide access to the data halls where data center information is stored. As shown in the figure below, a security trap is similar to an air lock. A person must first enter the security trap using their badge ID proximity bill of fare. After the person is within the security trap, facial recognition, fingerprints, or other biometric verifications are used to open the 2nd door. The user must repeat the process to go out the data hall.
17. A company is concerned with leaked and stolen corporate data on hard copies. Which information loss mitigation technique could assistance with this situation?
- stiff PC security settings
- stiff passwords
- shredding
- encryption
Hint/Explanation: Confidential data should be shredded when no longer required. Otherwise, a thief could remember discarded reports and gain valuable information.
18. Upon completion of a network security course, a student decides to pursue a career in cryptanalysis. What task would the student exist doing every bit a cryptanalyst?
- cracking code without access to the shared clandestine key
- creating hashing codes to authenticate data
- making and breaking hugger-mugger codes
- creating transposition and commutation ciphers
19. What command is used on a switch to set the port access entity type so the interface acts only as an authenticator and will non respond to any letters meant for a supplicant?
- dot1x pae authenticator
- hallmark port-control auto
- aaa authentication dot1x default group radius
- dot1x system-auth-control
Hint/Explanation: Sets the Port Access Entity (PAE) type.
dot1x pae [supplicant | authenticator | both]
- supplicant—The interface acts only equally a supplicant and does non respond to messages that are meant for an authenticator.
- authenticator-—The interface acts simply as an authenticator and does not respond to any messages meant for a supplicant.
- both—The interface behaves both as a supplicant and as an authenticator and thus does answer to all dot1x letters.
20. What are two disadvantages of using an IDS? (Choose ii.)
- The IDS does not terminate malicious traffic.
- The IDS works offline using copies of network traffic.
- The IDS has no touch on traffic.
- The IDS analyzes bodily forwarded packets.
- The IDS requires other devices to reply to attacks.
Hint/Explanation: The disadvantage of operating with mirrored traffic is that the IDS cannot terminate malicious unmarried-package attacks from reaching the target before responding to the attack. Also, an IDS frequently requires assistance from other networking devices, such equally routers and firewalls, to respond to an attack. An advantage of an IDS is that past working offline using mirrored traffic, it has no touch on traffic catamenia.
21. Refer to the exhibit. The ip verify source command is applied on untrusted interfaces. Which blazon of attack is mitigated by using this configuration?
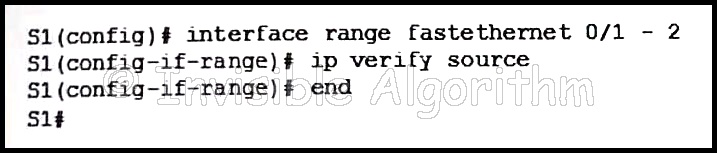
- DHCP spoofing
- DHCP starvation
- STP manipulation
- MAC and IP accost spoofing
Hint/Caption: To protect against MAC and IP address spoofing, apply the IP Source Guard security feature, using the ip verify source command, on untrusted ports.
22. What ports tin can receive forwarded traffic from an isolated port that is office of a PVLAN?
- other isolated ports and community ports
- simply promiscuous ports
- all other ports within the same customs
- only isolated ports
Hint/Explanation: PVLANs are used to provide Layer 2 isolation between ports within the same circulate domain. The level of isolation tin exist specified
with three types of PVLAN ports:
– Promiscuous ports that can frontwards traffic to all other ports
– Isolated ports that can only forward traffic to promiscuous ports
– Community ports that can frontwards traffic to other community ports and promiscuous ports
23. A user complains virtually being locked out of a device later too many unsuccessful AAA login attempts. What could be used by the network administrator to provide a secure hallmark access method without locking a user out of a device?
- Use the login filibuster command for authentication attempts.
- Use the login local control for authenticating user access.
- Utilise the aaa local hallmark attempts max-neglect global configuration manner control with a college number of acceptable failures.
- Use the none keyword when configuring the authentication method list.
Hint/Explanation: The login delay command introduces a delay between failed login attempts without locking the account. This provides a user with unlimited attempts at accessing a device without causing the user account to go locked and thus requiring ambassador intervention.
24. What are two drawbacks in assigning user privilege levels on a Cisco router? (Cull two.)
- Only a root user can add or remove commands.
- Privilege levels must exist fix to permit access control to specific device interfaces, ports, or slots.
- Assigning a command with multiple keywords allows access to all commands using those keywords.
- Commands from a lower level are e'er executable at a higher level.
- AAA must be enabled.
Hint/Explanation: Privilege levels may non provide desired flexibility and specificity because higher levels always inherit commands from lower levels, and commands with multiple keywords requite the user access to all commands available for each keyword. Privilege levels cannot specify access control to interfaces, ports, or slots. AAA is not required to set privilege levels, only is required in order to create role-based views. The function of root user does not exist in privilege levels.
25. Refer to the showroom. Which conclusion can be made from the show crypto map control output that is shown on R1?
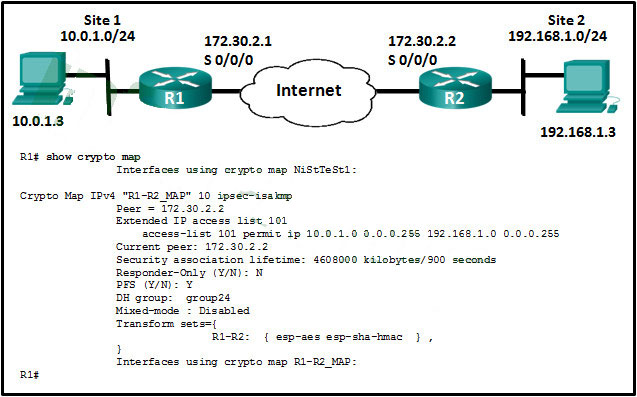
- The crypto map has not still been practical to an interface.
- The current peer IP address should exist 172.30.2.1.
- There is a mismatch betwixt the transform sets.
- The tunnel configuration was established and tin exist tested with extended pings.
Hint/Explanation: Co-ordinate to the show crypto map control output, all required SAs are in place, but no interface is currently using the crypto map. To consummate the tunnel configuration, the crypto map has to be applied to the outbound interface of each router.
26. What are two reasons to enable OSPF routing protocol hallmark on a network? (Choose 2.)
- to foreclose data traffic from beingness redirected and then discarded
- to ensure faster network convergence
- to provide information security through encryption
- to forbid redirection of information traffic to an insecure link
- to ensure more efficient routing
Hint/Explanation: The reason to configure OSPF hallmark is to mitigate against routing protocol attacks similar redirection of data traffic to an insecure link, and redirection of data traffic to discard information technology. OSPF authentication does not provide faster network convergence, more efficient routing, or encryption of information traffic.
27. Which three functions are provided past the syslog logging service? (Choose iii.)
- gathering logging information
- authenticating and encrypting data sent over the network
- retaining captured letters on the router when a router is rebooted
- specifying where captured information is stored
- distinguishing between data to be captured and information to be ignored
- setting the size of the logging buffer
Hint/Caption: Syslog operations include gathering information, selecting which type of data to capture, and directing the captured information to a storage location. The logging service stores letters in a logging buffer that is time-limited, and cannot retain the information when a router is rebooted. Syslog does not cosign or encrypt messages.
28. What two ICMPv6 message types must exist permitted through IPv6 access control lists to permit resolution of Layer 3 addresses to Layer 2 MAC addresses? (Cull two.)
- neighbor solicitations
- echo requests
- neighbor advertisements
- repeat replies
- router solicitations
- router advertisements
29. Which three services are provided through digital signatures? (Choose three.)
- accounting
- authenticity
- compression
- nonrepudiation
- integrity
- encryption
Hint/Caption: Digital signatures apply a mathematical technique to provide three basic security services:Integrity; Actuality; Nonrepudiation
xxx. A technician is to document the current configurations of all network devices in a college, including those in off-site buildings. Which protocol would be all-time to use to deeply access the network devices?
- FTP
- HTTP
- SSH
- Telnet
Hint/Explanation: Telnet sends passwords and other information in clear text, while SSH encrypts its data. FTP and HTTP do not provide remote device access for configuration purposes.
31. An administrator is trying to develop a BYOD security policy for employees that are bringing a wide range of devices to connect to the company network. Which three objectives must the BYOD security policy address? (Choose iii.)
- All devices must exist insured against liability if used to compromise the corporate network.
- All devices must accept open authentication with the corporate network.
- Rights and activities permitted on the corporate network must be divers.
- Safeguards must be put in place for any personal device existence compromised.
- The level of admission of employees when connecting to the corporate network must be defined.
- All devices should be allowed to attach to the corporate network flawlessly.
32. What is the function of the pass action on a Cisco IOS Zone-Based Policy Firewall?
- logging of rejected or dropped packets
- inspecting traffic between zones for traffic control
- tracking the state of connections between zones
- forwarding traffic from one zone to another
Hint/Explanation: The pass activity performed by Cisco IOS ZPF permits forwarding of traffic in a mode similar to the allow argument in an access control list.
33. Refer to the exhibit. Based on the security levels of the interfaces on ASA1, what traffic will be allowed on the interfaces?
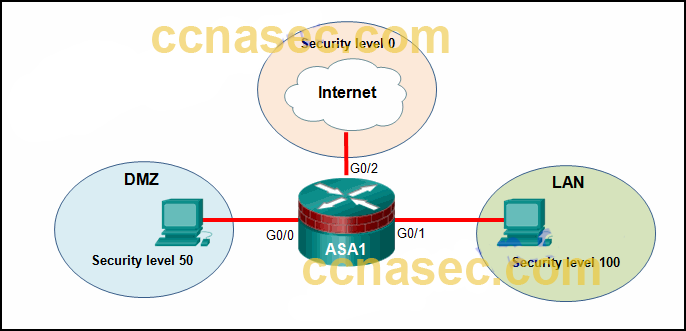
- Traffic from the Internet and DMZ can access the LAN.
- Traffic from the Net and LAN tin can access the DMZ.
- Traffic from the Cyberspace can admission both the DMZ and the LAN.
- Traffic from the LAN and DMZ can admission the Internet.
Hint/Explanation: ASA devices have security levels assigned to each interface that are not part of a configured ACL. These security levels allow traffic from more secure interfaces, such as security level 100, to access less secure interfaces, such as level 0. By default, they allow traffic from more than secure interfaces (higher security level) to access less secure interfaces (lower security level). Traffic from the less secure interfaces is blocked from accessing more secure interfaces.
34. What network testing tool tin be used to place network layer protocols running on a host?
- SIEM
- Nmap
- L0phtcrack
- Tripwire
35. In the implementation of security on multiple devices, how do ASA ACLs differ from Cisco IOS ACLs?
- Cisco IOS routers apply both named and numbered ACLs and Cisco ASA devices use only numbered ACLs.
- Cisco IOS ACLs are configured with a wildcard mask and Cisco ASA ACLs are configured with a subnet mask.
- Cisco IOS ACLs are processed sequentially from the top downwards and Cisco ASA ACLs are non processed sequentially.
- Cisco IOS ACLs utilise an implicit deny all and Cisco ASA ACLs finish with an implicit permit all.
Hint/Caption: The Cisco IOS ACLs are configured with a wildcard mask and the Cisco ASA ACLs are configured with a subnet mask. Both devices employ an implicit deny, top downwards sequential processing, and named or numbered ACLs.
36. Which statement describes an of import characteristic of a site-to-site VPN?
- It must exist statically gear up up.
- It is ideally suited for use by mobile workers.
- It requires using a VPN client on the host PC.
- Later the initial connection is established, information technology can dynamically change connectedness data.
- It is commonly implemented over dialup and cable modem networks.
Hint/Explanation: A site-to-site VPN is created between the network devices of 2 separate networks. The VPN is static and stays established. The internal hosts of the two networks have no knowledge of the VPN.
37. Which ii options are security best practices that help mitigate BYOD risks? (Cull two.)
- Utilize paint that reflects wireless signals and glass that prevents the signals from going exterior the building.
- Keep the device Os and software updated.
- Only allow devices that have been approved by the corporate Information technology team.
- Only plow on Wi-Fi when using the wireless network.
- Decrease the wireless antenna gain level.
- Use wireless MAC accost filtering.
Hint/Explanation: Many companies now back up employees and visitors attaching and using wireless devices that connect to and use the corporate wireless network. This practise is known as a bring-your-own-device policy or BYOD. Commonly, BYOD security practices are included in the security policy. Some best practices that mitigate BYOD risks include the post-obit:
Apply unique passwords for each device and business relationship.
Plow off Wi-Fi and Bluetooth connectivity when not being used. Only connect to trusted networks.
Keep the device OS and other software updated.
Backup whatsoever data stored on the device.
Subscribe to a device locator service with a remote wipe characteristic.
Provide antivirus software for canonical BYODs.
Use Mobile Device Management (MDM) software that allows IT teams to rail the device and implement security settings and software controls.
38. Refer to the showroom. A network ambassador configures AAA hallmark on R1. Which statement describes the result of the keyword unmarried-connexion in the configuration?
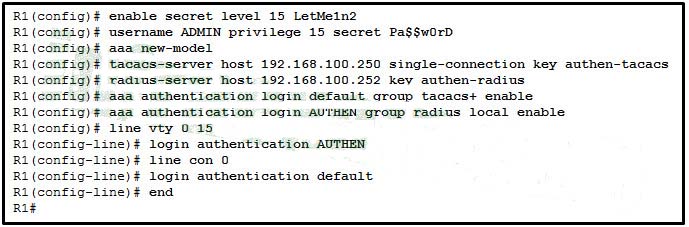
- R1 volition open a separate connection to the TACACS+ server for each user hallmark session.
- The hallmark performance is enhanced by keeping the connection to the TACACS+ server open.
- The TACACS+ server just accepts one successful endeavor for a user to authenticate with it.
- R1 will open a split connexion to the TACACS server on a per source IP address ground for each authentication session.
Hint/Explanation: The unmarried-connection keyword enhances TCP operation with TACACS+ past maintaining a unmarried TCP connexion for the life of the session. Without the unmarried-connection keyword, a TCP connexion is opened and closed per session.
39. A recently created ACL is not working every bit expected. The admin determined that the ACL had been practical entering on the interface and that was the incorrect management. How should the admin gear up this issue?
- Delete the original ACL and create a new ACL, applying it outbound on the interface.
- Add an association of the ACL outbound on the same interface.
- Gear up the ACE statements so that it works as desired entering on the interface.
- Remove the inbound association of the ACL on the interface and reapply it outbound.
40. What characteristic of the Snort term-based subscriptions is true for both the community and the subscriber rule sets?
- Both have a thirty-day delayed access to updated signatures.
- Both use Cisco Talos to provide coverage in advance of exploits.
- Both are fully supported by Cisco and include Cisco customer back up.
- Both offer threat protection against security threats.
Hint/Explanation: At that place are two types of term-based subscriptions:
– Customs Rule Set – Available for free, this subscription offers limited coverage against threats. The community rule ready focuses on reactive response to security threats versus proactive enquiry work. There is besides a xxx-24-hour interval delayed access to updated signatures significant that newest rule will be a minimum of thirty days quondam. In addition, in that location is no Cisco customer support available.
– Subscriber Rule Set – Available for a fee, this service provides the all-time protection confronting threats. Information technology includes coverage of advance exploits by using the research work of the Cisco Talos security experts. The Subscriber Rule Ready likewise provides the fastest access to updated signatures in response to a security incident or the proactive discovery of a new threat. This subscription is fully supported by Cisco.
41. A security analyst is configuring Snort IPS. The analyst has just downloaded and installed the Snort OVA file. What is the next step?
- Verify Snort IPS.
- Configure Virtual Port Group interfaces.
- Enable IPS globally or on desired interfaces.
- Activate the virtual services.
Hint/Explanation: To deploy Snort IPS on supported devices, perform the post-obit steps:
– Step 1. Download the Snort OVA file.
– Step 2. Install the OVA file.
– Stride 3. Configure Virtual Port Group interfaces.
– Step 4. Actuate the virtual services.
– Pace 5. Configure Snort specifics.
– Footstep six. Enable IPS globally or on desired interfaces.
– Step 7. Verify Snort IPS.
42. The security policy in a company specifies that employee workstations can initiate HTTP and HTTPS connections to outside websites and the return traffic is allowed. However, connections initiated from outside hosts are not allowed. Which parameter can be used in extended ACLs to run into this requirement?
- dscp
- precedence
- eq
- established
43. A researcher is comparing the differences between a stateless firewall and a proxy firewall. Which two additional layers of the OSI model are inspected past a proxy firewall? (Choose two.)
- Layer 3
- Layer 4
- Layer 5
- Layer 6
- Layer vii
Hint/Explanation: Packet filtering firewalls are usually office of a router firewall, which permits or denies traffic based on Layer 3 and Layer iv information. They are stateless firewalls that use a elementary policy table look-upwards that filters traffic based on specific criteria.
44. Refer to the showroom. A network ambassador is configuring a VPN between routers R1 and R2. Which commands would correctly configure a pre-shared key for the two routers?
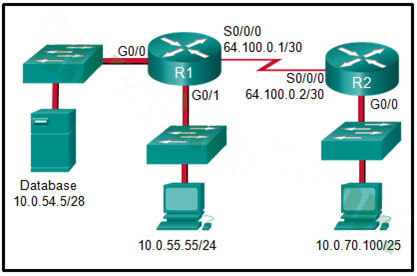
R1(config)# username R2 password 5tayout!
R2(config)# username R1 password 5tayout!
R1(config)# crypto isakmp central 5tayout! address 64.100.0.two
R2(config)# crypto isakmp central 5tayout! address 64.100.0.i
R1(config)# crypto isakmp key 5tayout! hostname R1
R2(config)# crypto isakmp primal 5tayout! hostname R2
R1(config-if)# ppp pap sent-username R1 password 5tayout!
R2(config-if)# ppp pap sent-username R2 password 5tayout!
45. Refer to the exhibit. Which statement is true nearly the effect of this Cisco IOS zone-based policy firewall configuration?
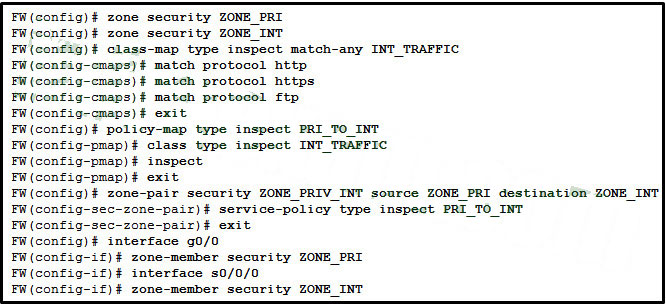
- The firewall will automatically drop all HTTP, HTTPS, and FTP traffic.
- The firewall will automatically let HTTP, HTTPS, and FTP traffic from s0/0/0 to g0/0 and volition rail the connections. Tracking the connection allows just return traffic to be permitted through the firewall in the opposite management.
- The firewall will automatically let HTTP, HTTPS, and FTP traffic from s0/0/0 to g0/0, merely will not track the land of connections. A corresponding policy must be practical to allow return traffic to be permitted through the firewall in the opposite direction.
- The firewall will automatically allow HTTP, HTTPS, and FTP traffic from g0/0 to s0/0/0 and will track the connections. Tracking the connectedness allows but
- return traffic to be permitted through the firewall in the contrary direction.
- The firewall will automatically allow HTTP, HTTPS, and FTP traffic from g0/0 to s0/0/0, but will non track the state of connections. A corresponding policy must be applied to let render traffic to be permitted through the firewall in the reverse direction.
46. Which privilege level has the most access to the Cisco IOS?
- level 0
- level 15
- level vii
- level 16
- level ane
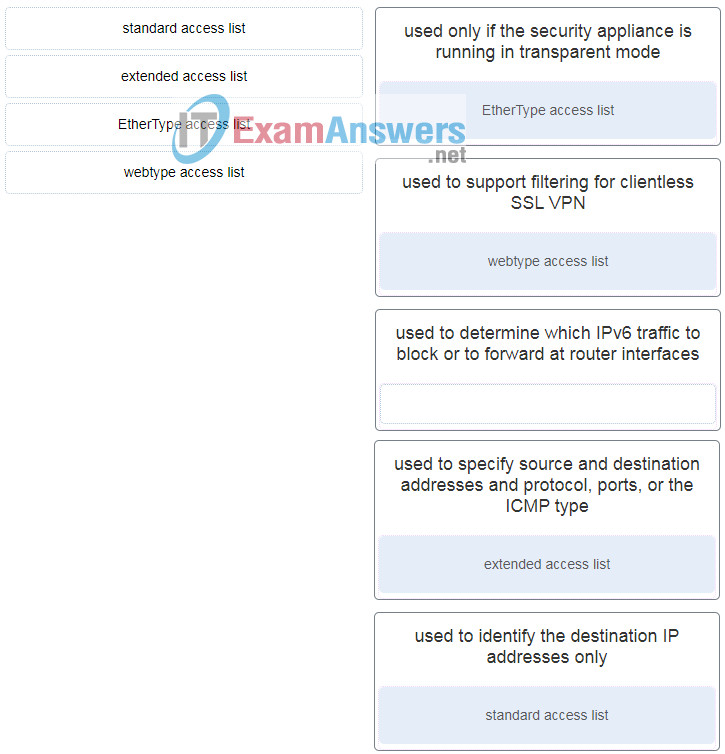
47. Match the type of ASA ACLs to the description. (Not all options are used.)
48. Which argument describes a difference between the Cisco ASA IOS CLI feature and the router IOS CLI characteristic?
- ASA uses the ? command whereas a router uses the help control to receive assistance on a brief description and the syntax of a command.
- To apply a prove command in a general configuration manner, ASA can use the command directly whereas a router will need to enter the do control before issuing the prove command.
- To complete a partially typed command, ASA uses the Ctrl+Tab key combination whereas a router uses the Tab fundamental.
- To indicate the CLI EXEC fashion, ASA uses the % symbol whereas a router uses the # symbol.
Hint/Caption: The ASA CLI is a proprietary Bone which has a similar expect and feel to the Cisco router IOS. Although it shares some common features with the router IOS, it has its unique features. For example, an ASA CLI command tin can be executed regardless of the current configuration fashion prompt. The IOS do control is non required or recognized. Both the ASA CLI and the router CLI use the # symbol to indicate the EXEC way. Both CLIs utilize the Tab key to consummate a partially typed control. Different from the router IOS, the ASA provides a help control that provides a brief command description and syntax for certain commands.
49. Refer to the exhibit. A network administrator is configuring AAA implementation on an ASA device. What does the option link3 indicate?
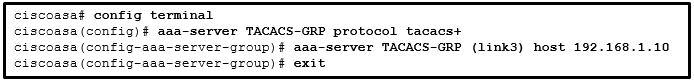
- the network name where the AAA server resides
- the specific AAA server proper noun
- the sequence of servers in the AAA server group
- the interface proper noun
fifty. What provides both secure segmentation and threat defence force in a Secure Data Middle solution?
- Cisco Security Director software
- AAA server
- Adaptive Security Appliance
- intrusion prevention organization
51. What are the three core components of the Cisco Secure Data Centre solution? (Choose iii.)
- mesh network
- secure segmentation
- visibility
- threat defense
- servers
- infrastructure
Hint/Explanation: Secure segmentation is used when managing and organizing data in a data center. Threat defence force includes a firewall and intrusion prevention system (IPS). Data center visibility is designed to simplify operations and compliance reporting by providing consequent security policy enforcement.
52. What are three characteristics of ASA transparent mode? (Choose three.)
- This mode does not support VPNs, QoS, or DHCP Relay.
- Information technology is the traditional firewall deployment style.
- This manner is referred to as a "bump in the wire."
- NAT can be implemented betwixt connected networks.
- In this fashion the ASA is invisible to an attacker.
- The interfaces of the ASA separate Layer three networks and crave IP addresses in different subnets.
53. What is needed to allow specific traffic that is sourced on the outside network of an ASA firewall to reach an internal network?
- ACL
- NAT
- dynamic routing protocols
- outside security zone level 0
Hint/Explanation: In guild to explicitly permit traffic from an interface with a lower security level to an interface with a higher security level, an ACL must exist configured. By default, traffic will only flow from a higher security level to a lower.
54. What will exist the consequence of failed login attempts if the following command is entered into a router?
- login block-for 150 attempts 4 within ninety
- All login attempts will be blocked for 150 seconds if in that location are 4 failed attempts within 90 seconds.
- All login attempts volition be blocked for 90 seconds if there are 4 failed attempts inside 150 seconds.
- All login attempts will exist blocked for ane.5 hours if there are iv failed attempts within 150 seconds.
- All login attempts will be blocked for 4 hours if there are 90 failed attempts within 150 seconds.
Hint/Caption: The components of the login block-for 150 attempts iv inside xc command are as follows:
The expression block-for 150 is the time in seconds that logins volition exist blocked.
The expression attempts iv is the number of failed attempts that will trigger the blocking of login requests.
The expression within 90 is the fourth dimension in seconds in which the 4 failed attempts must occur.
55. Which two tasks are associated with router hardening? (Choose two.)
- placing the router in a secure room
- disabling unused ports and interfaces
- installing the maximum amount of memory possible
- securing authoritative access
- using uninterruptible ability supplies
56. Which threat protection capability is provided by Cisco ESA?
- web filtering
- cloud access security
- spam protection
- Layer four traffic monitoring
Hint/Explanation: Electronic mail is a height assault vector for security breaches. Cisco ESA includes many threat protection capabilities for email such as spam protection, forged e-mail detection, and Cisco advanced phishing protection.
57. What are two security measures used to protect endpoints in the borderless network? (Choose two.)
- denylisting
- Snort IPS
- DLP
- DMZ
- rootkit
Hint/Explanation:
| Mensurate | Purpose |
|---|---|
| antimalware software | Protect endpoints from malware. |
| spam filtering | Prevent spam emails from reaching endpoints. |
| blocklisting | Foreclose endpoints from connecting to websites with bad reputations by immediately blocking connections based on the latest reputation intelligence. |
| information loss prevention (DLP) | Forestall sensitive information from being lost or stolen. |
58. Which iii types of traffic are allowed when the authentication port-command auto command has been issued and the client has not however been authenticated? (Choose three.)
- CDP
- 802.1Q
- IPsec
- TACACS+
- STP
- EAPOL
Hint/Caption: Until the workstation is authenticated, 802.1X admission control enables merely Extensible Authentication Protocol over LAN (EAPOL), Cisco Discovery Protocol (CDP), and Spanning Tree Protocol (STP) traffic through the port to which the workstation is connected. Subsequently hallmark succeeds, normal traffic can pass through the port.
59. Which statement describes a feature of the IKE protocol?
- It uses UDP port 500 to exchange IKE information between the security gateways.
- IKE Phase i tin can exist implemented in three unlike modes: main, ambitious, or quick.
- It allows for the manual of keys directly across a network.
- The purpose of IKE Phase two is to negotiate a security association betwixt two IKE peers.
threescore. Which action do IPsec peers take during the IKE Phase 2 exchange?
- exchange of DH keys
- negotiation of IPsec policy
- negotiation of IKE policy sets
- verification of peer identity
Hint/Explanation: The IKE protocol executes in two phases. During Phase one the two sides negotiate IKE policy sets, authenticate each other, and ready upward a secure channel. During the second stage IKE negotiates security associations between the peers.
61. What are two hashing algorithms used with IPsec AH to guarantee authenticity? (Choose two.)
- SHA
- RSA
- DH
- MD5
- AES
Hint/Explanation: The IPsec framework uses various protocols and algorithms to provide data confidentiality, data integrity, authentication, and secure key exchange. 2 popular algorithms used to ensure that data is not intercepted and modified (information integrity and authenticity) are MD5 and SHA.
62. Which control raises the privilege level of the ping command to 7?
- user exec ping level 7
- authorization exec ping level seven
- accounting exec level 7 ping
- privilege exec level vii ping
63. What is a feature of a role-based CLI view of router configuration?
- A CLI view has a command bureaucracy, with college and lower views.
- When a superview is deleted, the associated CLI views are deleted.
- A single CLI view can be shared within multiple superviews.
- Only a superview user can configure a new view and add or remove commands from the existing views.
Hint/Explanation: A CLI view has no command hierarchy, and therefore, no higher or lower views. Deleting a superview does not delete the associated CLI views. Only a root view user can configure a new view and add or remove commands from the existing views.
64. What is a limitation to using OOB management on a large enterprise network?
- Production traffic shares the network with management traffic.
- Terminal servers tin can take direct console connections to user devices needing management.
- OOB management requires the creation of VPNs.
- All devices appear to be attached to a single management network.
Hint/Explanation: OOB management provides a dedicated management network without production traffic. Devices within that network, such every bit last servers, accept direct console access for management purposes. Considering in-band management runs over the product network, secure tunnels or VPNs may be needed. Failures on the production network may not be communicated to the OOB network ambassador because the OOB management network may non exist affected
65. What engineering science has a function of using trusted third-party protocols to issue credentials that are accustomed as an authoritative identity?
- digital signatures
- hashing algorithms
- PKI certificates
- symmetric keys
Hint/Explanation: Digital certificates are used to bear witness the actuality and integrity of PKI certificates, but a PKI Certificate Potency is a trusted tertiary-party entity that issues PKI certificates. PKI certificates are public data and are used to provide authenticity, confidentiality, integrity, and nonrepudiation services that can scale to large requirements.
66. What is the best way to prevent a VLAN hopping assail?
- Disable body negotiation for trunk ports and statically set nontrunk ports as access ports.
- Disable STP on all nontrunk ports.
- Use VLAN 1 every bit the native VLAN on torso ports.
- Use ISL encapsulation on all trunk links.
67. What would be the primary reason an attacker would launch a MAC address overflow attack?
- and so that the switch stops forwarding traffic
- and so that legitimate hosts cannot obtain a MAC accost
- then that the attacker tin can meet frames that are destined for other hosts
- so that the attacker can execute arbitrary code on the switch
68. What is the main divergence between the implementation of IDS and IPS devices?
- An IDS can negatively bear on the parcel flow, whereas an IPS can not.
- An IDS needs to be deployed together with a firewall device, whereas an IPS tin supervene upon a firewall.
- An IDS would permit malicious traffic to pass before it is addressed, whereas an IPS stops it immediately.
- An IDS uses signature-based engineering to find malicious packets, whereas an IPS uses profile-based engineering science.
Hint/Explanation: An IPS is deployed in inline mode and will not let malicious traffic to enter the internal network without commencement analyzing information technology. An reward of this is that it can stop an set on immediately. An IDS is deployed in promiscuous mode. It copies the traffic patterns and analyzes them offline, thus information technology cannot finish the assail immediately and it relies on another device to take further deportment once it detects an attack. Existence deployed in inline mode, an IPS can negatively touch on the traffic catamenia. Both IDS and IPS can utilise signature-based technology to detect malicious packets. An IPS cannot supplant other security devices, such equally firewalls, considering they perform unlike tasks.
69. Which attack is divers as an attempt to exploit software vulnerabilities that are unknown or undisclosed by the vendor?
- cipher-day
- Trojan horse
- creature-strength
- man-in-the-middle
70. Match the network monitoring applied science with the description.
71. What are the three signature levels provided past Snort IPS on the 4000 Series ISR? (Cull 3.)
- security
- drib
- turn down
- connectivity
- inspect
- counterbalanced
72. What are three attributes of IPS signatures? (Choose three.)
- action
- length
- trigger
- type
- depth
- function
Hint/Caption: IPS signatures have iii distinctive attributes:
- type
- trigger (alarm)
- activeness
73. Match each IPS signature trigger category with the clarification.
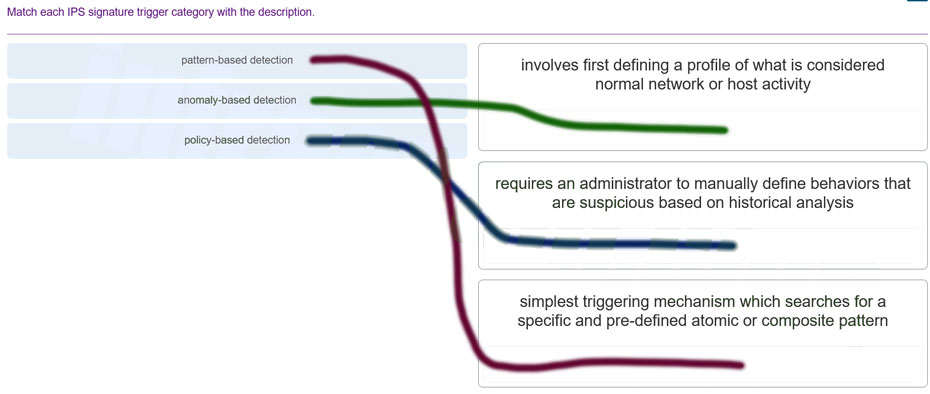
74. Which two features are included past both TACACS+ and RADIUS protocols? (Choose two.)
- SIP support
- countersign encryption
- 802.1X support
- separate authentication and authorization processes
- utilization of transport layer protocols
Hint/Explanation: Both TACACS+ and RADIUS support countersign encryption (TACACS+ encrypts all communication) and use Layer 4 protocol (TACACS+ uses TCP and RADIUS uses UDP). TACACS+ supports separation of authentication and authority processes, while RADIUS combines authentication and say-so as one process. RADIUS supports remote access engineering, such equally 802.1x and SIP; TACACS+ does not.
75. What function is provided by the RADIUS protocol?
- RADIUS provides encryption of the consummate packet during transfer.
- RADIUS provides separate AAA services.
- RADIUS provides separate ports for authorisation and accounting.
- RADIUS provides secure communication using TCP port 49.
Hint/Explanation: When an AAA user is authenticated, RADIUS uses UDP port 1645 or 1812 for authentication and UDP port 1646 or 1813 for accounting. TACACS provides separate say-so and accounting services. When a RADIUS client is authenticated, it is also authorized. TACACS provides secure connectivity using TCP port 49. RADIUS hides passwords during transmission and does non encrypt the complete bundle.
76. What are three characteristics of the RADIUS protocol? (Choose three.)
- utilizes TCP port 49
- uses UDP ports for authentication and bookkeeping
- supports 802.1X and SIP
- separates the authentication and authorization processes
- encrypts the entire torso of the bundle
- is an open RFC standard AAA protocol
Hint/Caption: RADIUS is an open up-standard AAA protocol using UDP port 1645 or 1812 for hallmark and UDP port 1646 or 1813 for accounting. It combines hallmark and authorization into one procedure; thus, a password is encrypted for transmission while the residuum of the packet will exist sent in plain text. RADIUS offers the expedited service and more comprehensive bookkeeping desired by remote-access providers but provides lower security and less potential for customization than TACACS+.
77. Which zone-based policy firewall zone is organization-divers and applies to traffic destined for the router or originating from the router?
- local zone
- within zone
- self zone
- system zone
- outside zone
78. What are two benefits of using a ZPF rather than a Classic Firewall? (Choose two.)
- ZPF allows interfaces to exist placed into zones for IP inspection.
- The ZPF is not dependent on ACLs.
- Multiple inspection actions are used with ZPF.
- ZPF policies are easy to read and troubleshoot.
- With ZPF, the router will allow packets unless they are explicitly blocked.
Hint/Explanation: There are several benefits of a ZPF:
– It is not dependent on ACLs.
– The router security posture is to block unless explicitly immune.
– Policies are like shooting fish in a barrel to read and troubleshoot with C3PL.
– I policy affects any given traffic, instead of needing multiple ACLs and inspection deportment.
In improver, an interface cannot be simultaneously configured equally a security zone member and for IP inspection.
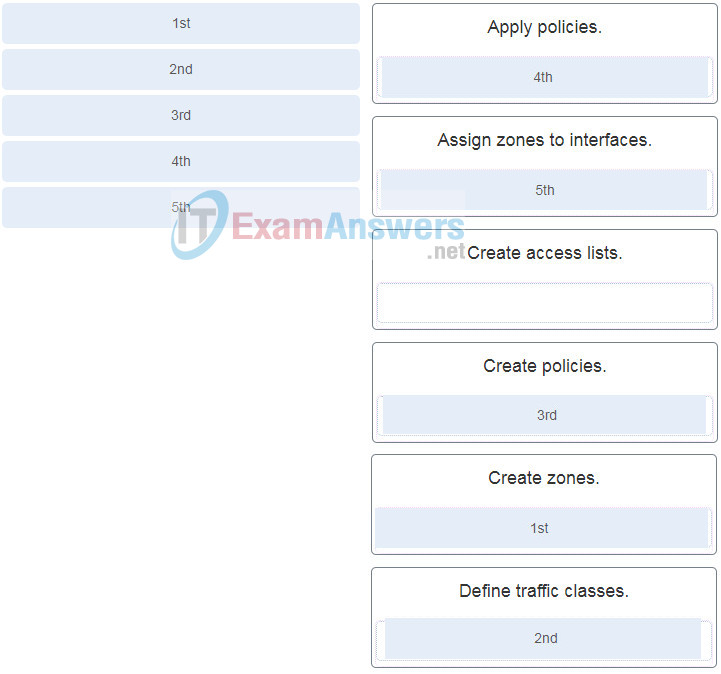
79. Place the steps for configuring zone-based policy (ZPF) firewalls in social club from first to terminal. (Non all options are used.)
80. Refer to the exhibit. Which two conclusions tin be drawn from the syslog bulletin that was generated by the router? (Cull ii.)
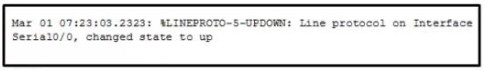
- This bulletin resulted from an unusual error requiring reconfiguration of the interface.
- This message indicates that service timestamps have been configured.
- This bulletin indicates that the interface inverse state five times.
- This bulletin is a level v notification message.
- This bulletin indicates that the interface should be replaced.
Hint/Explanation: The message is a level 5 notification message as shown in the %LINEPROTO-five section of the output. Letters reporting the link condition are common and do not require replacing the interface or reconfiguring the interface. The engagement and time displayed at the beginning of the message indicates that service timestamps have been configured on the router.
81. Which two types of hackers are typically classified as grey hat hackers? (Choose two.)
- hacktivists
- cyber criminals
- vulnerability brokers
- script kiddies
- land-sponsored hackers
Hint/Caption: Grayness hat hackers may do unethical or illegal things, simply not for personal gain or to cause impairment. Hacktivists utilise their hacking as a course of political or social protest, and vulnerability brokers hack to uncover weaknesses and report them to vendors. Depending on the perspective 1 possesses, land-sponsored hackers are either white hat or blackness hat operators. Script kiddies create hacking scripts to cause harm or disruption. Cyber criminals use hacking to obtain financial proceeds by illegal means.
82. How does a firewall handle traffic when it is originating from the private network and traveling to the DMZ network?
- The traffic is selectively denied based on service requirements.
- The traffic is usually permitted with picayune or no restrictions.
- The traffic is selectively permitted and inspected.
- The traffic is usually blocked.
Hint/Explanation: With a three interface firewall design that has internal, external, and DMZ connections, typical configurations include the following:
– Traffic originating from DMZ destined for the internal network is normally blocked.
– Traffic originating from the DMZ destined for external networks is typically permitted based on what services are being used in the DMZ.
– Traffic originating from the internal network destined from the DMZ is usually inspected and allowed to return.
– Traffic originating from external networks (the public network) is typically allowed in the DMZ but for specific services.
83. Which two protocols generate connexion information within a state tabular array and are supported for stateful filtering? (Cull two.)
- ICMP
- UDP
- DHCP
- TCP
- HTTP
84. Which type of firewall is supported past most routers and is the easiest to implement?
- next generation firewall
- stateless firewall
- stateful firewall
- proxy firewall
- Tripwire
- L0phtcrack
- Nessus
- Metasploit
- Use statistical assay to eliminate the most mutual encryption keys.
- Use a keyspace large plenty that it takes likewise much coin and too much fourth dimension to conduct a successful attack.
- Use an algorithm that requires the attacker to have both ciphertext and plaintext to conduct a successful attack.
- Use frequency analysis to ensure that the most popular letters used in the language are not used in the zero message.
- Letters of the message are replaced by some other letter that is a set number of places away in the alphabet.
- Messages of the message are rearranged randomly.
- Letters of the message are rearranged based on a predetermined blueprint.
- Words of the message are substituted based on a predetermined pattern.
- complication of the hashing algorithm
- the use of 3DES over AES
- secrecy of the keys
- secrecy of the algorithm
- negotiation of the ISAKMP policy
- negotiation of the IPsec SA policy
- detection of interesting traffic
- authentication of peers
- RSA
- Diffie-Hellman
- DES
- AES
Hint/Caption: Bundle Filtering (Stateless) Firewall uses a simple policy tabular array look-up that filters traffic based on specific criteria and is considered the easiest firewall to implement.
85. What network testing tool would an ambassador apply to assess and validate system configurations confronting security policies and compliance standards?
Hint/Explanation: Tripwire – This tool assesses and validates IT configurations against internal policies, compliance standards, and security best practices.
86. How do modernistic cryptographers defend against fauna-force attacks?
Hint/Caption: In a brute-forcefulness attack, an attacker tries every possible key with the decryption algorithm knowing that somewhen i of them will work. To defend against the creature-force attacks, mod cryptographers take as an objective to have a keyspace (a set of all possible keys) large plenty so that it takes too much money and as well much time to accomplish a beast-force assail. A security policy requiring passwords to be changed in a predefined interval further defend against the creature-force attacks. The thought is that passwords will have been changed before an assailant exhausts the keyspace.
87. How does a Caesar nix work on a message?
52. What is the main factor that ensures the security of encryption of mod algorithms?
Hint/Explanation: With most modernistic algorithms, successful decryption requires cognition of the appropriate cryptographic keys. This means that the security of encryption lies in the secrecy of the keys, not the algorithm.
88. What is the side by side step in the establishment of an IPsec VPN after IKE Phase ane is complete?
Hint/Explanation: Establishing an IPsec tunnel involves 5 steps:
detection of interesting traffic defined by an ACL
IKE Phase 1 in which peers negotiate ISAKMP SA policy
IKE Phase two in which peers negotiate IPsec SA policy
Creation of the IPsec tunnel
Termination of the IPsec tunnel
89. Refer to the exhibit. What algorithm will be used for providing confidentiality?
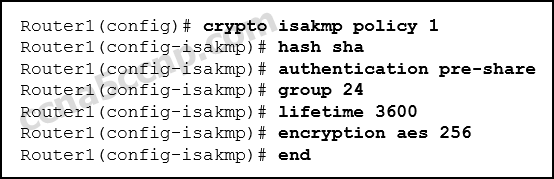
Hint/Caption: The IPsec framework uses diverse protocols and algorithms to provide data confidentiality, information integrity, authentication, and secure key exchange. Two popular algorithms that are used to ensure that data is non intercepted and modified (data integrity) are MD5 and SHA. AES is an encryption protocol and provides data confidentiality. DH (Diffie-Hellman) is an algorithm that is used for key exchange. RSA is an algorithm used for authentication.
90. After issuing a show run control, an analyst notices the following command:
crypto ipsec transform-set MYSET esp-aes 256 esp-md5-hmac
What is the purpose of this control?
- It establishes the set of encryption and hashing algorithms used to secure the data sent through an IPsec tunnel.
- It defines the default ISAKMP policy list used to establish the IKE Phase 1 tunnel.
- Information technology establishes the criteria to force the IKE Phase 1 negotiations to begin.
- Information technology indicates that IKE will be used to establish the IPsec tunnel for protecting the traffic.
91. Which algorithm can ensure data integrity?
- RSA
- AES
- MD5
- PKI
Hint/Explanation: Data integrity guarantees that the message was non altered in transit. Integrity is ensured by implementing either of the Secure Hash Algorithms (SHA-2 or SHA-3). The MD5 message digest algorithm is all the same widely in use.
92. A visitor implements a security policy that ensures that a file sent from the headquarters function to the branch office can only be opened with a predetermined code. This code is changed every twenty-four hours. Which two algorithms tin exist used to achieve this task? (Cull two.)
- HMAC
- MD5
- 3DES
- SHA-ane
- AES
Hint/Explanation: The task to ensure that only authorized personnel tin open up a file is data confidentiality, which can exist implemented with encryption. AES and 3DES are two encryption algorithms. HMAC can exist used for ensuring origin authentication. MD5 and SHA-1 can be used to ensure data integrity.
93. A network technician has been asked to design a virtual private network between two branch routers. Which blazon of cryptographic key should exist used in this scenario?
- hash key
- symmetric key
- disproportionate key
- digital signature
Hint/Caption: A symmetric key requires that both routers have access to the secret key that is used to encrypt and decrypt exchanged information.
94. Which two options tin can limit the information discovered from port scanning? (Choose 2.)
- intrusion prevention system
- firewall
- hallmark
- passwords
- encryption
Hint/Explanation: Using an intrusion prevention organisation (IPS) and firewall tin limit the information that can be discovered with a port scanner. Authentication, encryption, and passwords provide no protection from loss of information from port scanning.
95. An administrator discovers that a user is accessing a newly established website that may be detrimental to company security. What action should the administrator take first in terms of the security policy?
- Enquire the user to stop immediately and inform the user that this constitutes grounds for dismissal.
- Create a firewall rule blocking the respective website.
- Revise the AUP immediately and become all users to sign the updated AUP.
- Immediately suspend the network privileges of the user.
96. If AAA is already enabled, which three CLI steps are required to configure a router with a specific view? (Choose three.)
- Create a superview using the parser view view-name command.
- Associate the view with the root view.
- Assign users who tin can use the view.
- Create a view using the parser view view-name command.
- Assign a secret password to the view.
- Assign commands to the view.
Hint/Explanation: There are five steps involved to create a view on a Cisco router.
1) AAA must be enabled.
2) the view must be created.
3) a underground countersign must be assigned to the view.
4) commands must be assigned to the view.
5) view configuration mode must be exited.
97. Refer to the showroom. A network ambassador configures a named ACL on the router. Why is at that place no output displayed when the bear witness command is issued?
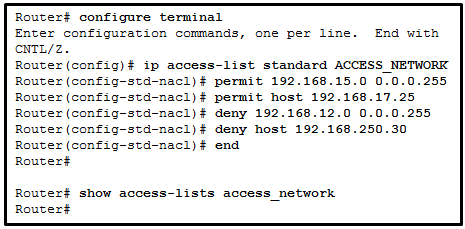
- The ACL is not activated.
- The ACL name is instance sensitive.
- The ACL has not been applied to an interface.
- No packets have matched the ACL statements yet.
98. ACLs are used primarily to filter traffic. What are 2 additional uses of ACLs? (Choose two.):
- specifying internal hosts for NAT
- identifying traffic for QoS
- specifying source addresses for authentication
- reorganizing traffic into VLANs
- filtering VTP packets
Hint/Explanation: ACLs are used to filter traffic to determine which packets will be permitted or denied through the router and which packets volition exist subject field to policy-based routing. ACLs can also exist used to identify traffic that requires NAT and QoS services. Prefix lists are used to control which routes will be redistributed or advertised to other routers.
99. What two features are added in SNMPv3 to accost the weaknesses of previous versions of SNMP? (Choose 2.)
- authentication
- authorization with community cord priority
- bulk MIB objects retrieval
- ACL management filtering
- encryption
100. What network testing tool is used for password auditing and recovery?
- Nessus
- Metasploit
- L0phtcrack
- SuperScan
101. Which type of firewall makes use of a server to connect to destination devices on behalf of clients?
- packet filtering firewall
- proxy firewall
- stateless firewall
- stateful firewall
Hint/Explanation: An awarding gateway firewall, also called a proxy firewall, filters information at Layers 3, 4, 5, and 7 of the OSI model. It uses a proxy server to connect to remote servers on behalf of clients. Remote servers will see only a connectedness from the proxy server, non from the individual clients.
102. Refer to the exhibit. What will exist displayed in the output of the show running-config object command later on the exhibited configuration commands are entered on an ASA 5506-X?
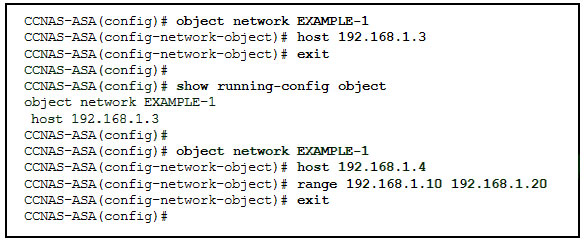
- host 192.168.i.4
- range 192.168.one.ten 192.168.1.xx
- host 192.168.1.three, host 192.168.ane.4, and range 192.168.i.10 192.168.one.20
- host 192.168.1.iii
- host 192.168.one.3 and host 192.168.i.four
- host 192.168.1.iv and range 192.168.1.x 192.168.1.20
Hint/Caption: The show running-config object command is used to display or verify the IP accost/mask pair inside the object. In that location tin only exist i statement in the network object. Entering a 2d IP address/mask pair will supersede the existing configuration.
103. Refer to the exhibit. Co-ordinate to the command output, which three statements are truthful most the DHCP options entered on the ASA? (Choose three.)
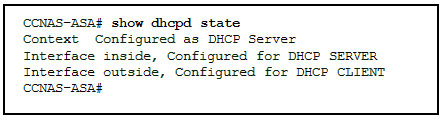
- The dhcpd address [ start-of-pool ]-[ end-of-pool ] within command was issued to enable the DHCP server.
- The dhcpd address [ offset-of-puddle ]-[ terminate-of-puddle ] inside command was issued to enable the DHCP client.
- The dhcpd enable inside command was issued to enable the DHCP server.
- The dhcpd auto-config exterior command was issued to enable the DHCP client.
- The dhcpd automobile-config exterior control was issued to enable the DHCP server.
- The dhcpd enable inside control was issued to enable the DHCP client.
104. Which two statements describe the characteristics of symmetric algorithms? (Choose two.)
- They are unremarkably used with VPN traffic.
- They use a pair of a public fundamental and a individual key.
- They are commonly implemented in the SSL and SSH protocols.
- They provide confidentiality, integrity, and availability.
- They are referred to as a pre-shared key or underground key.
Hint/Explanation: Symmetric encryption algorithms employ the same key (also called shared secret) to encrypt and decrypt the information. In contrast, asymmetric encryption algorithms use a pair of keys, ane for encryption and another for decryption.
105. A web server ambassador is configuring access settings to crave users to authenticate first earlier accessing certain web pages. Which requirement of information security is addressed through the configuration?
- availability
- integrity
- scalability
- confidentiality
Hint/Explanation: Confidentiality ensures that data is accessed only by authorized individuals. Authentication volition help verify the identity of the individuals.
106. The use of 3DES within the IPsec framework is an example of which of the 5 IPsec building blocks?
- authentication
- nonrepudiation
- integrity
- Diffie-Hellman
- confidentiality
Hint/Explanation: The IPsec framework consists of five building blocks. Each edifice cake performs a specific securty function via specific protocols. The function of providing confidentiality is provided by protocols such every bit DES, 3DES, and AES.
107. What function is provided by Snort as part of the Security Onion?
- to generate network intrusion alerts by the use of rules and signatures
- to normalize logs from various NSM data logs and then they can be represented, stored, and accessed through a mutual schema
- to display total-bundle captures for analysis
- to view pcap transcripts generated by intrusion detection tools
Hint/Caption: Snort is an open up source network intrusion prevention organisation (NIPS) and network intrusion detection system (NIDS) adult by Sourcefire. It has the ability to perform real fourth dimension traffic analysis and packet logging on Internet Protocol (IP) networks and can also exist used to detect probes or attacks.
108. What are 2 drawbacks to using HIPS? (Cull two.)
- With HIPS, the success or failure of an attack cannot be readily adamant.
- With HIPS, the network administrator must verify support for all the different operating systems used in the network.
- HIPS has difficulty constructing an accurate network picture or coordinating events that occur across the entire network.
- If the network traffic stream is encrypted, HIPS is unable to access unencrypted forms of the traffic.
- HIPS installations are vulnerable to fragmentation attacks or variable TTL attacks.
109. In an AAA-enabled network, a user issues the configure terminal control from the privileged executive mode of functioning. What AAA role is at work if this command is rejected?
- dominance
- authentication
- auditing
- accounting
Hint/Explanation: Hallmark must ensure that devices or end users are legitimate. Authorization is concerned with assuasive and disallowing authenticated users admission to sure areas and programs on the network. The configure terminal command is rejected because the user is not authorized to execute the command.
110. A company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin grouping. Which component is addressed in the AAA network service framework?
- automation
- accounting
- authentication
- potency
Hint/Caption: After a user is successfully authenticated (logged into the server), the potency is the process of determining what network resources the user can admission and what operations (such equally read or edit) the user tin perform.
111. What is a characteristic of a DMZ zone?
- Traffic originating from the inside network going to the DMZ network is non permitted.
- Traffic originating from the outside network going to the DMZ network is selectively permitted.
- Traffic originating from the DMZ network going to the within network is permitted.
- Traffic originating from the inside network going to the DMZ network is selectively permitted.
Hint/Explanation: The characteristics of a DMZ zone are every bit follows:
Traffic originating from the inside network going to the DMZ network is permitted.
Traffic originating from the outside network going to the DMZ network is selectively permitted.
Traffic originating from the DMZ network going to the inside network is denied.
112. Which measure tin a security analyst accept to perform constructive security monitoring against network traffic encrypted by SSL technology?
- Use a Syslog server to capture network traffic.
- Deploy a Cisco SSL Appliance.
- Require remote access connections through IPsec VPN.
- Deploy a Cisco ASA.
113. What type of network security test can detect and report changes made to network systems?
- vulnerability scanning
- network scanning
- integrity checking
- penetration testing
Hint/Explanation: Integrity checking is used to detect and report changes made to systems. Vulnerability scanning is used to find weaknesses and misconfigurations on network systems. Network scanning is used to discover available resources on the network.
114. What network security testing tool has the ability to provide details on the source of suspicious network activity?
- SIEM
- SuperScan
- Zenmap
- Tripwire
115. Refer to the exhibit. Port security has been configured on the Fa 0/12 interface of switch S1. What activity will occur when PC1 is attached to switch S1 with the applied configuration?
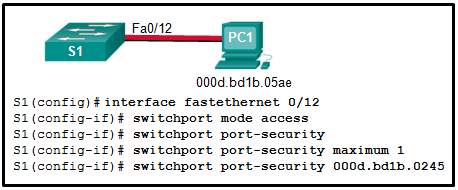
- Frames from PC1 volition be forwarded since the switchport port-security violation command is missing.
- Frames from PC1 will be forwarded to its destination, and a log entry will exist created.
- Frames from PC1 will be forwarded to its destination, but a log entry volition not be created.
- Frames from PC1 will cause the interface to close down immediately, and a log entry will be made.
- Frames from PC1 will be dropped, and at that place will be no log of the violation.
- Frames from PC1 volition be dropped, and a log message volition be created.
Hint/Explanation: Manual configuration of the single immune MAC address has been entered for port fa0/12. PC1 has a unlike MAC address and when fastened will cause the port to shut downwards (the default activeness), a log message to exist automatically created, and the violation counter to increment. The default activity of shutdown is recommended because the restrict choice might fail if an set on is underway.
116. What security countermeasure is effective for preventing CAM table overflow attacks?
- DHCP snooping
- Dynamic ARP Inspection
- IP source guard
- port security
Hint/Explanation: Port security is the most effective method for preventing CAM table overflow attacks. Port security gives an administrator the power to manually specify what MAC addresses should exist seen on given switch ports. It provides a method for limiting the number of MAC addresses that can be dynamically learned over a switch port.
117. What are 2 examples of DoS attacks? (Choose two.)
- port scanning
- SQL injection
- ping of death
- phishing
- buffer overflow
Hint/Caption: The buffer overflow and ping of death DoS attacks exploit arrangement memory-related flaws on a server by sending an unexpected corporeality of data or malformed data to the server.
118. Which method is used to identify interesting traffic needed to create an IKE phase 1 tunnel?
- transform sets
- a permit access listing entry
- hashing algorithms
- a security association
Updating….
Refer to the showroom. A network administrator has configured NAT on an ASA device. What type of NAT is used?
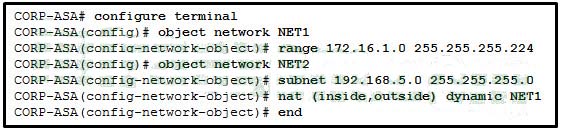
- inside NAT
- static NAT
- bidirectional NAT
- exterior NAT
Hint/Caption: NAT can be deployed on an ASA using one of these methods:
inside NAT – when a host from a higher-security interface has traffic destined for a lower-security interface and the ASA translates the internal host address to a global address
exterior NAT – when traffic from a lower-security interface destined for a host on the higher-security interface is translated
bidirectional NAT – when both inside NAT and outside NAT are used together
Because the nat command is applied so that the within interface is mapped to the outside interface, the NAT blazon is inside. As well, the dynamic keyword in the nat command indicates that it is a dynamic mapping.
Match the security technology with the description.
Lucifer the security term to the appropriate clarification. (Not all options are used.)
Match the IPS alarm blazon to the description.
A network analyst is configuring a site-to-site IPsec VPN. The analyst has configured both the ISAKMP and IPsec policies. What is the next step?
- Configure the hash as SHA and the authentication as pre-shared.
- Apply the crypto map to the appropriate outbound interfaces.
- Issue the show crypto ipsec sa control to verify the tunnel.
- Verify that the security feature is enabled in the IOS.
Which Security Measure Is Typically Found Both Inside And Outside A Data Center Facility?,
Source: https://ccnasec.com/network-security-version-1-network-security-1-0-final-exam-answers.html
Posted by: johnsonbleanto1988.blogspot.com


0 Response to "Which Security Measure Is Typically Found Both Inside And Outside A Data Center Facility?"
Post a Comment